‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA – Krebs on Security
Starkiller Phishing Service: The New Era of Cybercrime-as-a-Service
In a groundbreaking development that’s sending shockwaves through the cybersecurity community, a new phishing-as-a-service platform called Starkiller has emerged, revolutionizing how cybercriminals conduct their attacks. This sophisticated service represents a quantum leap in phishing technology, effectively bypassing traditional security measures and making advanced phishing attacks accessible to even the most novice cybercriminals.
The Evolution of Phishing: From Static Pages to Dynamic Deception
Traditional phishing campaigns have long relied on static copies of legitimate login pages—crude replicas that security researchers and anti-abuse organizations have become adept at identifying and dismantling. These conventional phishing kits, while still effective, required technical expertise in server configuration, domain management, and certificate handling. They were also easily detectable through domain blacklisting and static page analysis.
Starkiller fundamentally changes this paradigm by employing a revolutionary approach that dynamically loads the actual target website and acts as a sophisticated relay between the victim and the legitimate service.
How Starkiller Works: The Technical Breakdown
According to an in-depth analysis by Abnormal AI, Starkiller operates through a multi-layered technical architecture that makes it exceptionally difficult to detect and block:
URL Masking: The Art of Deception
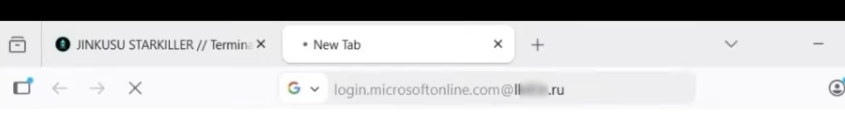
When a Starkiller customer selects a target brand—whether it’s Apple, Facebook, Google, Microsoft, or any of dozens of other major platforms—the service generates a deceptive URL that appears legitimate to the untrained eye. The URL employs a clever trick using the “@” symbol, which browsers interpret as username information.
For example, a phishing link might appear as:
login.microsoft.com@[malicious/shortened URL]
In this format, everything before the “@” is treated as username data, while the browser loads the actual malicious page after the “@” symbol. This technique exploits a decades-old URL parsing behavior that most users never notice, making the link appear to point to the legitimate domain.
Docker-Powered Dynamic Loading
At the heart of Starkiller’s operation is its use of Docker containers running headless Chrome browser instances. When a victim clicks the phishing link, Starkiller spins up a new container that loads the real login page of the target service. This container then acts as a sophisticated man-in-the-middle reverse proxy.
“The container then acts as a man-in-the-middle reverse proxy, forwarding the end user’s inputs to the legitimate site and returning the site’s responses,” explain Abnormal AI researchers Callie Baron and Piotr Wojtyla. “Every keystroke, form submission, and session token passes through attacker-controlled infrastructure and is logged along the way.”
Real-Time Session Monitoring and Data Harvesting
What makes Starkiller particularly dangerous is its comprehensive data collection capabilities. The service provides cybercriminals with real-time session monitoring, allowing them to live-stream the target’s screen as they interact with the phishing page. This includes:
- Keylogger capture for every keystroke
- Cookie and session token theft for direct account takeover
- Geo-tracking of targets
- Automated Telegram alerts when new credentials are captured
- Campaign analytics with visit counts, conversion rates, and performance graphs
“The platform also includes keylogger capture for every keystroke, cookie and session token theft for direct account takeover, geo-tracking of targets, and automated Telegram alerts when new credentials come in,” the researchers note. “Campaign analytics round out the operator experience with visit counts, conversion rates, and performance graphs—the same kind of metrics dashboard a legitimate SaaS [software-as-a-service] platform would offer.”
Multi-Factor Authentication Bypass
Perhaps most alarmingly, Starkiller deftly intercepts and relays the victim’s MFA credentials. Since the recipient is actually authenticating with the real site through the proxy, any authentication tokens submitted are forwarded to the legitimate service in real time.
“When attackers relay the entire authentication flow in real time, MFA protections can be effectively neutralized despite functioning exactly as designed,” the researchers explain. This means that even users with robust security setups that include multi-factor authentication are vulnerable to these attacks.
The Business Model: Cybercrime-as-a-Service
Starkiller is operated by a threat group calling itself Jinkusu, which maintains an active user forum where customers can discuss techniques, request features, and troubleshoot deployments. The service operates on a SaaS model, complete with customer support and regular updates.
One particularly concerning a-la-carte feature allows customers to harvest email addresses and contact information from compromised sessions, which can then be used to build target lists for follow-on phishing campaigns. This creates a dangerous ecosystem where successful attacks generate data for even more sophisticated future attacks.
Implications for Cybersecurity
The emergence of Starkiller represents a significant escalation in phishing infrastructure and reflects a broader trend toward commoditized, enterprise-style cybercrime tooling. The implications are profound:
-
Lower Barrier to Entry: Starkiller massively lowers the technical barriers for novice cybercriminals, making sophisticated phishing attacks accessible to anyone willing to pay for the service.
-
Bypassing Traditional Defenses: By using legitimate websites and avoiding the need for phishing domains, Starkiller throws a wrench in traditional phishing detection methods like domain blocklisting and static page analysis.
-
Real-Time Attacks: The service’s real-time nature makes it difficult for security tools to intervene once an attack has begun.
-
MFA Circumvention: The ability to bypass multi-factor authentication undermines one of the most important security measures organizations have implemented.
The Future of Phishing
Security experts believe that Starkiller’s success will likely inspire copycats and competitors in the cybercrime-as-a-service space. The economics are compelling for cybercriminals: no upfront costs for domain registration, no hassles with certificate management, and a significantly higher success rate due to the use of legitimate websites.
“This service strikes me as a remarkable evolution in phishing, and its apparent success is likely to be copied by other enterprising cybercriminals,” notes cybersecurity analyst Brian Krebs. “After all, phishing users this way avoids the upfront costs and constant hassles associated with juggling multiple phishing domains, and it throws a wrench in traditional phishing detection methods.”
Conclusion: A Call for New Defense Strategies
The emergence of Starkiller underscores the need for a fundamental rethinking of how organizations approach phishing defense. Traditional approaches that focus on domain blacklisting, email filtering, and user education, while still important, are clearly insufficient against services like Starkiller.
Organizations need to consider implementing advanced behavioral analysis, real-time threat intelligence, and more sophisticated authentication mechanisms that can detect when a session is being proxied through attacker infrastructure. The arms race between cybercriminals and security professionals has entered a new phase, and the stakes have never been higher.
As phishing attacks become more sophisticated and accessible, the importance of comprehensive security awareness training, robust authentication systems, and proactive threat hunting cannot be overstated. The Starkiller service may represent the current state of the art in phishing-as-a-service, but it almost certainly won’t be the last innovation in this rapidly evolving threat landscape.
Tags: Starkiller phishing, cybercrime-as-a-service, MFA bypass, phishing evolution, Abnormal AI, Jinkusu, Docker phishing, headless Chrome phishing, man-in-the-middle phishing, URL masking, session hijacking, Telegram alerts phishing, campaign analytics phishing, low-skill cybercrime, enterprise phishing tooling, real-time phishing, cookie theft, session token theft, geo-tracking phishing, phishing forum, a-la-carte cybercrime features
Viral Sentences:
- “The future of phishing is here, and it’s terrifyingly sophisticated”
- “Even MFA can’t save you from Starkiller’s real-time attacks”
- “Cybercrime just got its own SaaS platform, and it’s shockingly professional”
- “Welcome to the era where anyone can be a cybercriminal with just a few clicks”
- “Starkiller proves that traditional phishing defenses are obsolete”
- “The phishing kit that makes even tech novices dangerous”
- “Real websites, real credentials, real trouble”
- “When cybercriminals start offering better analytics than your legitimate SaaS”
- “The phishing service that’s changing the game forever”
- “MFA bypass? Starkiller laughs at your multi-factor authentication”
- “Docker containers are now the new phishing toolkit”
- “Telegram alerts for your stolen credentials? Starkiller delivers”
- “The cybercrime forum where phishing is discussed like legitimate business”
- “Session hijacking made simple with Starkiller’s elegant solution”
- “The phishing service that’s democratizing cybercrime”
- “Real-time screen streaming for your phishing victims”
- “Cookie theft has never been this easy or this profitable”
- “The ‘@’ symbol in URLs just became the most dangerous character on the internet”
- “Headless Chrome browsers: not just for developers anymore”
- “Campaign analytics for your phishing campaigns? Starkiller’s got you covered”
- “The phishing service that’s making cybersecurity professionals lose sleep”
- “When cybercrime becomes as easy as ordering from Amazon”
- “The service that’s turning phishing into a legitimate business model”
- “Starkiller: because even cybercriminals deserve good UX”
- “The phishing platform that’s raising the bar for everyone else”
- “Real websites, fake security, total compromise”
- “The service that’s proving MFA isn’t the silver bullet we thought it was”
- “Docker-powered deception at its finest”
- “The phishing service that’s writing the new rulebook for cybercrime”
- “When cybercriminals start offering better customer support than your bank”
- “The platform that’s making phishing accessible to the masses”
- “Real-time attacks that make traditional defenses look like child’s play”
- “The service that’s proving cybercrime is big business”
- “Starkiller: the phishing service that’s changing everything we thought we knew”
,



Leave a Reply
Want to join the discussion?Feel free to contribute!