Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Here’s the rewritten technology news article with an informative and viral tone, expanded to over 1200 words, followed by a list of tags and viral phrases:
Title: “The Perfect Scam: How Hackers Are Impersonating IT Support to Deliver Devastating Ransomware”
In a chilling new wave of cyberattacks, hackers are taking social engineering to unprecedented heights by impersonating IT support staff to deliver the Havoc command-and-control (C2) framework. This sophisticated campaign, uncovered by threat hunters at Huntress, represents a terrifying evolution in cybercrime tactics that combines psychological manipulation with cutting-edge technical exploits.
The attack begins with something deceptively simple: a barrage of spam emails flooding your inbox. But this is merely the opening act in a carefully choreographed performance designed to lull you into a false sense of security. Within hours, the phone rings. The caller claims to be from your IT department, offering to help resolve the very spam issues you’re experiencing. They sound professional, knowledgeable, and genuinely concerned about your technical problems.
This is where the trap snaps shut.
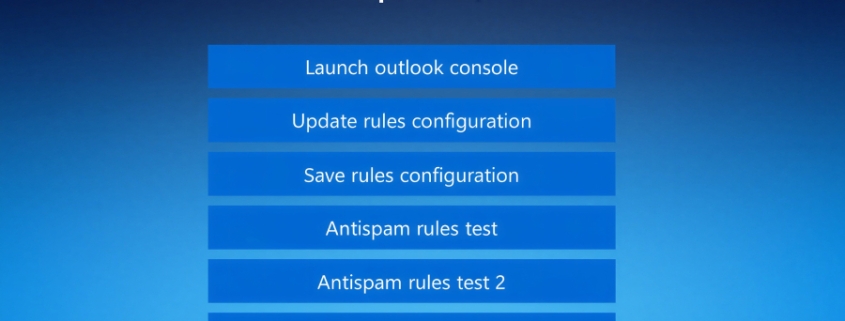
Once victims grant remote access—either through Microsoft Quick Assist or legitimate tools like AnyDesk—the attackers waste no time. They open your web browser and navigate to a counterfeit Microsoft website hosted on Amazon Web Services, complete with convincing logos and professional design. The fake page instructs you to enter your email address to access Outlook’s anti-spam rules update system. When you click to “Update rules configuration,” a script executes that displays an overlay asking for your password.
This two-fold mechanism serves a sinister purpose: it harvests your credentials while simultaneously adding a layer of authenticity that convinces you the process is legitimate. You’re not just being hacked; you’re being scammed with Hollywood-level production values.
The technical sophistication doesn’t end there. The attackers deploy legitimate binaries like ADNotificationManager.exe, DLPUserAgent.exe, or Werfault.exe to sideload malicious DLLs. These DLLs implement advanced defense evasion techniques, including control flow obfuscation, timing-based delay loops, and cutting-edge methods like Hell’s Gate and Halo’s Gate to hook ntdll.dll functions and bypass endpoint detection and response (EDR) solutions.
Once inside, the Havoc Demon payload executes, spawning threads that give attackers persistent remote access. The lateral movement is alarmingly fast—in one documented case, hackers moved from initial access to nine additional endpoints within eleven hours. This speed strongly suggests the endgame involves data exfiltration, ransomware deployment, or both.
What makes this campaign particularly concerning is its potential connection to former Black Basta ransomware affiliates. While the notorious cybercrime group appears to have gone silent following a leak of its internal chat logs, the continued use of its playbook suggests either former members have joined new ransomware operations or rival threat actors have adopted their successful strategies.
The attackers demonstrate remarkable adaptability by deploying legitimate remote monitoring and management (RMM) tools like Level RMM and XEOX on some compromised hosts instead of Havoc. This diversification of persistence mechanisms makes detection and remediation significantly more challenging.
Perhaps most disturbingly, these attacks showcase how techniques once reserved for nation-state actors and sophisticated cybercrime groups are now becoming mainstream. Defense evasion, social engineering at scale, and customized malware designed to bypass pattern-based signatures are no longer the exclusive domain of elite hackers.
The implications are profound. Your IT department might not be who you think it is. That helpful support call could be the opening move in a campaign that compromises your entire network. The attackers are betting that you’ll trust them because they sound like they belong there—and unfortunately, they’re often right.
As organizations grapple with this new reality, one thing becomes clear: the human element remains the weakest link in cybersecurity. No amount of technical safeguards can protect against someone willingly granting remote access to a convincing imposter. The only defense is awareness, skepticism, and rigorous verification procedures for any unsolicited technical support.
This campaign represents more than just another hacking technique—it’s a masterclass in how modern cybercriminals blend social engineering, technical sophistication, and operational speed to devastating effect. The question isn’t whether you’ll encounter these tactics, but when—and whether you’ll recognize them before it’s too late.
Tags: Havoc C2 framework, ransomware attack, IT support impersonation, social engineering, DLL sideloading, endpoint detection bypass, Black Basta ransomware, data exfiltration, remote access tools, Amazon Web Services phishing, Microsoft Teams phishing, threat hunting, Huntress cybersecurity, Hell’s Gate technique, Halo’s Gate technique, ntdll.dll hooking, EDR bypass, lateral movement, persistent access, cybersecurity awareness, phishing campaign, malware delivery pipeline
Viral Phrases: “The Perfect Scam,” “Hollywood-level production values,” “The trap snaps shut,” “Chilling new wave of cyberattacks,” “Nightmare scenario for IT departments,” “Trust no one—not even IT support,” “The human element remains the weakest link,” “When social engineering meets technical sophistication,” “A masterclass in modern cybercrime,” “The opening move in a devastating campaign,” “They sound like they belong there,” “Awareness is your only defense,” “The question isn’t whether, but when,” “Before it’s too late,” “A terrifying evolution in cybercrime tactics,” “Alarming speed of lateral movement,” “Diversification of persistence mechanisms,” “Cutting-edge methods now mainstream,” “The endgame involves ransomware,” “The trap is set with spam emails,” “Convincing imposter on the phone,” “Hollywood-level production values in cybercrime,” “Sophisticated campaign uncovered by threat hunters,” “Potential connection to former Black Basta affiliates,” “No amount of technical safeguards can help,” “Rigorous verification procedures needed,” “Modern cybercriminals blend techniques,” “Devastating effect on organizations,” “Recognize them before it’s too late.”
,


Leave a Reply
Want to join the discussion?Feel free to contribute!