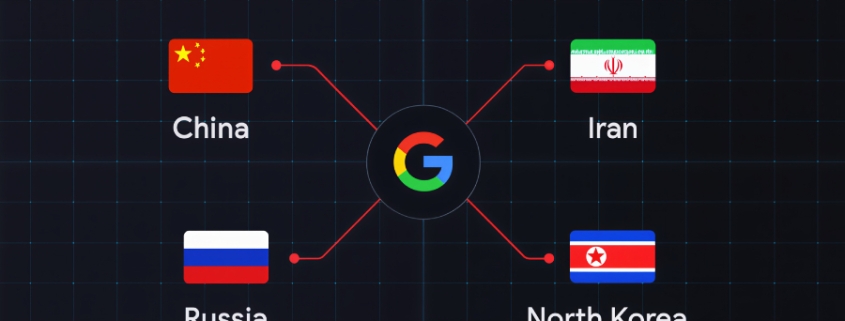
Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations
Google Threat Intelligence Group Exposes Global Cyber Onslaught Against Defense Industrial Base
In a sobering revelation that underscores the escalating cyber warfare landscape, Google’s Threat Intelligence Group (GTIG) has unveiled a comprehensive analysis detailing how state-sponsored actors, hacktivist collectives, and criminal syndicates from China, Iran, North Korea, and Russia are systematically targeting the Defense Industrial Base (DIB) sector with unprecedented sophistication and persistence.
The Four-Pronged Assault Strategy
GTIG’s exhaustive investigation reveals that adversarial targeting of the DIB sector operates through four critical thematic vectors:
-
Battlefield Technology Exploitation: Actors are specifically targeting defense entities deploying cutting-edge technologies on active battlefields, particularly in the Russia-Ukraine conflict.
-
Employment Process Infiltration: North Korean and Iranian operatives are directly approaching employees and exploiting hiring processes to embed malicious access points within defense organizations.
-
Edge Device Manipulation: Chinese-affiliated groups are leveraging edge devices and network appliances as initial access pathways, effectively bypassing traditional perimeter defenses.
-
Supply Chain Vulnerability Exploitation: Manufacturing sector breaches are creating cascading risks throughout the defense supply chain, amplifying attack surfaces exponentially.
“Modern warfare increasingly depends on autonomous vehicles and drones,” GTIG emphasized in their official statement. “The ‘evasion of detection’ trend continues unabated as threat actors focus on single endpoints and individuals, or execute intrusions designed to completely circumvent endpoint detection and response (EDR) tools.”
The Threat Actor Landscape: A Who’s Who of Digital Warfare
Russian Operations
APT44 (Sandworm): This GRU-affiliated group has demonstrated remarkable sophistication by targeting Telegram and Signal encrypted messaging applications. After securing physical access to devices during ground operations in Ukraine, Sandworm deployed a Windows batch script called WAVESIGN to decrypt and exfiltrate data from Signal’s desktop application. The operation showcases the convergence of physical and cyber warfare tactics.
TEMP.Vermin (UAC-0020): This threat cluster has weaponized malware families including VERMONSTER, SPECTRUM, and FIRMACHAGENT, deploying them through meticulously crafted lure content centered around drone production, anti-drone defense systems, and video surveillance security infrastructure.
UNC5125 (FlyingYeti/UAC-0149): Operating with surgical precision, this group has conducted highly targeted campaigns against frontline drone units. Their methodology involves distributing malware like MESSYFORK (COOKBOX) through Google Forms questionnaires designed to reconnoiter prospective drone operators. The malware was successfully delivered to an Unmanned Aerial Vehicle (UAV) operator based in Ukraine.
UNC5792 (UAC-0195): This sophisticated actor has exploited secure messaging applications to target Ukrainian military and government entities, extending their reach to individuals and organizations in Moldova, Georgia, France, and the United States. Their signature tactic involves weaponizing Signal’s device linking feature to hijack victim accounts entirely.
UNC4221 (UAC-0185): Employing tactics remarkably similar to UNC5792, this group has targeted secure messaging applications used by Ukrainian military personnel. They’ve developed an Android malware called STALECOOKIE that mimics Ukraine’s battlefield management platform DELTA, specifically designed to steal browser cookies. Additionally, they’ve leveraged ClickFix techniques to deliver the TINYWHALE downloader, which subsequently drops MeshAgent remote management software.
UNC5976: This Russian espionage cluster executed a sophisticated phishing campaign delivering malicious Remote Desktop Protocol (RDP) connection files configured to communicate with actor-controlled domains impersonating Ukrainian telecommunications companies.
UNC5976: This Russian espionage cluster executed a sophisticated phishing campaign delivering malicious Remote Desktop Protocol (RDP) connection files configured to communicate with actor-controlled domains impersonating Ukrainian telecommunications companies.
UNC6096: Operating through WhatsApp, this Russian espionage cluster utilized DELTA-related themes to deliver malicious LNK shortcuts within archive files that download secondary payloads. Their Android-focused attacks deployed GALLGRAB malware capable of collecting locally stored files, contact information, and potentially encrypted user data from specialized battlefield applications.
UNC5114: This suspected Russian espionage cluster distributed a variant of the commercial Android malware CraxsRAT by masquerading it as an update for Kropyva, a critical combat control system extensively used in Ukrainian military operations.
North Korean Operations
APT45 (Andariel): This North Korean threat actor has systematically targeted South Korean defense, semiconductor, and automotive manufacturing entities using SmallTiger malware, demonstrating the regime’s expanding cyber capabilities beyond traditional espionage.
APT43 (Kimsuky): Likely leveraging infrastructure mimicking German and U.S. defense-related entities, this group has deployed a sophisticated backdoor called THINWAVE, indicating advanced social engineering capabilities and infrastructure development.
UNC2970 (Lazarus Group): This notorious North Korean cyber collective conducted Operation Dream Job, targeting aerospace, defense, and energy sectors. They’ve incorporated artificial intelligence tools into their reconnaissance operations, marking a significant evolution in their targeting methodology.
Iranian Operations
UNC1549 (Nimbus Manticore): This Iranian nexus threat actor has systematically targeted aerospace, aviation, and defense industries across the Middle East using malware families including MINIBIKE, TWOSTROKE, DEEPROOT, and CRASHPAD. Their operations mirror Lazarus Group-style Dream Job campaigns, employing sophisticated social engineering to trick users into executing malware or surrendering credentials under the guise of legitimate employment opportunities.
UNC6446: This Iranian-affiliated threat actor utilized resume builder and personality test applications to distribute custom malware targeting aerospace and defense verticals across the United States and Middle East, demonstrating innovative social engineering approaches.
Chinese Operations
APT5 (Keyhole Panda/Mulberry Typhoon): This Chinese threat actor has targeted current and former employees of major aerospace and defense contractors using meticulously tailored phishing lures, indicating deep reconnaissance capabilities and understanding of organizational structures.
UNC3236 (Volt Typhoon): This Chinese nexus group has conducted reconnaissance against publicly hosted login portals of North American military and defense contractors while utilizing the ARCMAZE obfuscation framework to conceal their operational origin, making attribution significantly more challenging.
UNC6508: This China-nexus threat cluster executed a sophisticated attack against a U.S.-based research institution in late 2023. They exploited a REDCap vulnerability to drop custom malware named INFINITERED, capable of persistent remote access and credential theft by intercepting the application’s software upgrade process.
The Operational Relay Box Revolution
Google’s analysis uncovered a particularly concerning development: China-nexus threat groups are increasingly utilizing operational relay box (ORB) networks for reconnaissance against defense industrial targets. This technique fundamentally complicates detection and attribution efforts.
ORBs provide threat actors with multiple strategic advantages:
- Traffic Routing: Ability to route malicious traffic through home or commercial networks
- Blending Capability: Seamless integration with regular network traffic patterns
- Geofencing Circumvention: Effective bypassing of geographic-based security controls
- Perimeter Pre-positioning: Strategic positioning ahead of cyber attacks
- Resilience: High resistance to takedown attempts due to scalable network architecture
The Broader Implications
“The defense industrial base is under a state of constant, multi-vector siege,” Google’s analysis concludes grimly. “Financially motivated actors carry out extortion against this sector and the broader manufacturing base, like many of the other verticals they target for monetary gain.”
The campaigns against defense contractors in Ukraine, threats to or exploitation of defense personnel, the persistent volume of intrusions by China-nexus actors, and the hack, leak, and disruption of the manufacturing base represent some of the leading threats to this critical industry today.
As cyber warfare continues to evolve at breakneck speed, the defense industrial base finds itself at the epicenter of a global cyber conflict that shows no signs of abating. The sophistication, persistence, and coordination demonstrated by these threat actors suggest we are witnessing the emergence of a new paradigm in state-sponsored cyber operations—one where the lines between espionage, sabotage, and warfare have become increasingly blurred.
Tags:
Cyber Warfare, Defense Industrial Base, State-Sponsored Hacking, Google Threat Intelligence, APT Groups, Malware Campaigns, Ukraine Conflict, Supply Chain Security, Operational Relay Boxes, Cyber Espionage
Viral Phrases:
“The defense industrial base is under a state of constant, multi-vector siege”
“Threat actors focus on single endpoints and individuals”
“Completely circumvent endpoint detection and response (EDR) tools”
“Converging physical and cyber warfare tactics”
“Social engineering at unprecedented scale”
“The emergence of a new paradigm in state-sponsored cyber operations”
“Where the lines between espionage, sabotage, and warfare have become increasingly blurred”
“Constant, multi-vector siege”
“Blending with regular network traffic”
“Geofencing circumvention”
“Strategic positioning ahead of cyber attacks”
“High resistance to takedown attempts”
“Persistent volume of intrusions”
“Hack, leak, and disruption”
“Critical industry today”
“Escalating cyber warfare landscape”
“Systematic targeting with unprecedented sophistication”
“Global cyber onslaught”
“Digital warfare landscape”
“Cyber conflict that shows no signs of abating”
,



Leave a Reply
Want to join the discussion?Feel free to contribute!