New phishing hacks aren’t sloppy—they’re personalized
The Rise of Personalized Scams: How Fraudsters Are Using Your Data to Target You
In the ever-evolving landscape of online threats, scammers are getting smarter, more sophisticated, and alarmingly personal. The days of generic “You’ve won a million dollars!” emails are fading into history. Today’s cybercriminals are crafting highly targeted attacks that use your personal information to trick you into handing over money, data, or both.
I recently spoke with Steve Grobman, Chief Technology Officer at McAfee, to understand how these personalized scams work and what we can do to protect ourselves. What I discovered was both fascinating and deeply concerning.
The Evolution of Digital Deception
Scams have always been a part of the digital world, but the game has changed dramatically. Today’s fraudsters are leveraging artificial intelligence, data breaches, and social engineering techniques to create scams that feel incredibly authentic and specific to their targets.
“The shift toward personalization is driven by the availability of data and the tools to process it,” Grobman explained. “Scammers are essentially becoming data-driven marketers, but instead of selling products, they’re selling deception.”
Three Levels of Personalized Scams
According to Grobman, personalized scams generally fall into three categories, each more sophisticated than the last.
The “General” Personalized Scam
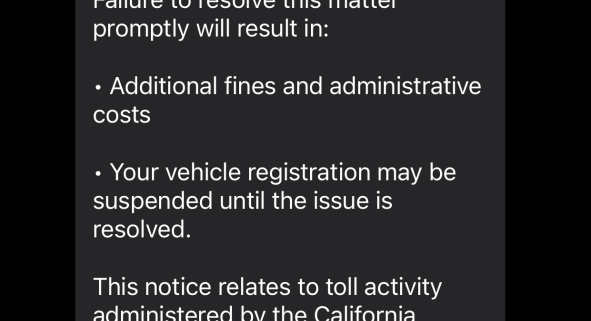
These scams cast a wide net but add just enough personalization to seem legitimate. A prime example is the modern toll road scam. While early versions simply claimed you had unpaid tolls, today’s versions mention your specific regional toll authority and use your area code to make the message seem authentic.
“I’ve seen messages that reference specific toll systems by name, using information derived from your phone number’s area code,” Grobman noted. “It’s a simple trick, but it significantly increases the scam’s credibility.”
These scams rely on AI to quickly gather regional information and incorporate it into messages. The scammer doesn’t need to know much about you personally—just enough to make a connection that feels relevant.
The “Specific” Personalized Scam
This is where things get more concerning. These scams use information from data breaches and leaks to create messages that address you by name and reference specific details about your life.
Grobman calls these “fill in the blank” scams. “Imagine a message that starts with your name and references a specific government agency or service you might actually use,” he said. “For example, ‘John, the California Department of Motor Vehicles has revoked your registration due to unpaid fees.'”
The extra information allows for additional customization that can make even savvy internet users pause and question whether the message might be real.
The “Hyperpersonalized” Scam
This is the most insidious category—and the one that keeps security experts up at night. These scams target your lifestyle, habits, and interests with surgical precision.
“Scammers use your browsing history, clicked links, and online behavior to figure out what you care about,” Grobman explained. “Then they exploit those interests with laser-focused precision.”
For instance, if you’ve shown interest in weight loss products, you might receive a message about a revolutionary new weight loss drug. The message feels relevant because it is—it’s based on your actual online behavior.
These scams can also take weeks or months to develop, like romance scams where the fraudster builds trust by weaving personal details into conversations before eventually asking for money or favors.
The AI Factor
Artificial intelligence is the secret weapon behind this personalization revolution. AI tools allow scammers to quickly analyze vast amounts of data and craft messages that sound natural and convincing.
“AI can help scammers figure out regional information, generate natural-sounding text, and even create fake but convincing documents,” Grobman said. “What used to take hours of manual work can now be done in seconds.”
The technology has democratized scam creation, allowing even less sophisticated criminals to launch highly targeted attacks.
What To Do If You’ve Been Scammed
If you realize you’ve fallen for a scam, the first thing to remember is: you’re not alone. Even security professionals can be fooled.
“Take a deep breath,” Grobman advised. “It’s normal to feel overwhelmed by emotions like shock, embarrassment, or shame. Those feelings are common and valid.”
The next step is to seek help immediately. The FTC’s consumer advice page provides comprehensive guidance for different scam scenarios.
Address the immediate problem first. If you shared credit card information, contact your bank right away. If you revealed sensitive personal information like your Social Security number, place a security freeze on your credit reports immediately.
Don’t neglect your emotional well-being either. Talk to friends, family, or even your employer’s IT department. Sometimes just getting perspective from others can help you navigate the situation more effectively.
Protecting Yourself in the Age of Personalized Scams
The good news is that while scams are getting more sophisticated, so are the tools to fight them. Here’s what you can do to protect yourself:
Use robust security software. Keep antivirus software active on all your devices. Windows Security is a solid free option that Microsoft automatically keeps updated.
Be selective about what you install. Only download apps from official app stores and be cautious about browser extensions.
Keep everything updated. Software updates often include security patches that protect against known vulnerabilities.
Use a password manager. Strong, unique passwords for every account are your first line of defense.
Think before you click. Be skeptical of unsolicited messages, even if they seem to know personal details about you.
Limit what you share online. The less information available about you, the harder it is for scammers to personalize their attacks.
The Bottom Line
As Grobman put it, “Scammers are business owners. They do what makes money.” As long as personalized scams continue to be profitable, they’ll keep evolving and becoming more sophisticated.
The race between scammers and security experts is escalating, with both sides leveraging AI and other advanced technologies. But the most powerful tool in this fight is still human awareness and caution.
By understanding how these scams work and taking proactive steps to protect yourself, you can stay one step ahead of the fraudsters—no matter how personal their attacks become.
Tags
Personalized scams, AI-powered fraud, data breaches, phishing attacks, toll scams, romance scams, social engineering, cybersecurity, online fraud, identity theft, scam prevention, digital security, McAfee, Steve Grobman, online safety, fraud detection, scam awareness, personal data protection, cyber threats, internet security, financial fraud, email scams, text message scams, online deception, security software, password managers, data privacy, scam recovery, FTC consumer protection, digital hygiene, online vigilance, AI in cybersecurity, fraud prevention, scam education, online trust, personal information security, cyber defense, digital fraud trends, modern scams, targeted attacks, online threats, security awareness, fraud tactics, data-driven scams, personalized attacks, online risk management, digital safety tips, scam identification, security best practices, online protection, fraud awareness, digital security trends, scam evolution, personalized fraud, online safety guide, cybersecurity tips, fraud prevention strategies, digital defense, online security measures, scam protection, personal data safety, online fraud prevention, security awareness training, digital privacy, online scam detection, fraud education, cybersecurity awareness, online safety education, digital security guide, scam prevention tips, online security awareness, fraud detection tools, personal security, online fraud trends, digital protection, cybersecurity education, online safety measures, fraud prevention education, digital security awareness, online protection tips, security best practices guide, online safety training, digital fraud prevention, cybersecurity training, online security education, fraud awareness training, digital safety awareness, online protection guide, security awareness guide, online fraud education, digital security training, cybersecurity guide, online safety tips, fraud prevention guide, digital protection tips, online security guide, security awareness tips, online safety resources, fraud detection guide, digital security resources, online protection resources, security awareness resources, online fraud resources, digital protection resources, cybersecurity resources, online safety resources, fraud prevention resources, digital security resources, online security resources, security awareness resources, online fraud resources, digital protection resources, cybersecurity resources, online safety resources, fraud prevention resources, digital security resources
,



Leave a Reply
Want to join the discussion?Feel free to contribute!