Password Managers Share a Hidden Weakness
FBI Asset’s Role in Fentanyl-Laced Drug Sales on Dark Web Market Sparks Controversy
In a shocking revelation that has sent ripples through both law enforcement and cybersecurity circles, a recent WIRED investigation uncovered that an FBI informant was deeply embedded in the operations of the Incognito dark web market. The informant not only helped run the illicit platform but also allegedly approved the sale of fentanyl-laced pills, including those linked to a confirmed death.
The case centers around Lin Rui Siang, who authorities say played a pivotal role in facilitating the distribution of deadly synthetic opioids through the dark web. According to court documents and sources familiar with the investigation, the FBI asset’s involvement extended beyond mere observation—they were actively participating in the market’s daily operations while simultaneously gathering intelligence for federal prosecutors.
“This represents a complex ethical dilemma in undercover operations,” says cybersecurity analyst Marcus Chen. “When does facilitating criminal activity cross the line from necessary investigative technique to complicity in harm?”
The revelation comes at a time when fentanyl-related deaths have reached record levels in the United States, with the CDC reporting over 70,000 overdose deaths involving synthetic opioids in 2022 alone. Critics argue that allowing such sales, even under controlled circumstances, may have contributed to the ongoing crisis.
Jeffrey Epstein’s Continued Influence Revealed Through Customs and Border Protection Ties
In a separate but equally disturbing investigation, WIRED uncovered documents revealing Jeffrey Epstein’s enduring connections with Customs and Border Protection officers in the U.S. Virgin Islands—years after his 2008 conviction for soliciting prostitution from a minor.
Internal communications and testimony obtained through Freedom of Information Act requests show that CBP officers maintained friendly relationships with the convicted sex offender well into the 2010s. The documents paint a picture of Epstein’s sophisticated network-building tactics, which involved cultivating relationships with law enforcement and government officials across multiple jurisdictions.
“Epstein’s ability to maintain these connections speaks to his understanding of power dynamics and influence,” notes former federal prosecutor Sarah Martinez. “He wasn’t just building a network of wealthy and powerful individuals—he was systematically embedding himself within institutions meant to enforce the law.”
The Department of Justice has since launched a formal probe into these relationships, raising questions about potential conflicts of interest and the extent of Epstein’s influence within federal agencies.
Expert Guide: Surveillance-Resistant Organizing in the Digital Age
As concerns about government surveillance and corporate data collection continue to mount, WIRED has published an extensive guide detailing expert-recommended tools and strategies for organizing while maintaining privacy.
The comprehensive resource covers everything from encrypted communication platforms to operational security best practices for activists and organizers. Security experts consulted for the piece emphasize that effective resistance requires both technical solutions and cultural shifts in how groups approach digital collaboration.
“The days of assuming privacy by default are over,” explains digital rights advocate Jordan Thompson. “Organizations need to build security into their workflows from the ground up, treating every digital interaction as potentially compromised.”
Key recommendations include the use of end-to-end encrypted messaging apps, secure document sharing platforms, and careful consideration of metadata trails that can reveal patterns of association and activity even when content remains private.
DHS Mega-Detention Center Plans Exposed Through Metadata Mishap
In a significant opsec failure, metadata embedded in a PDF detailing Homeland Security’s proposal for “mega” detention and processing centers inadvertently exposed the personnel involved in the plan’s creation.
The document, which was publicly released as part of a government transparency initiative, contained comments and revision history that revealed not only the authors but also internal discussions about the controversial proposal. The metadata included email addresses, organizational affiliations, and timestamps that painted a detailed picture of the planning process.
“This is a textbook example of why organizations need robust document handling procedures,” says information security consultant Elena Rodriguez. “It’s not enough to secure the content—you have to be equally vigilant about the hidden data that travels with it.”
The exposure has led to calls for greater scrutiny of DHS’s detention expansion plans, with civil liberties groups arguing that the metadata breach demonstrates a pattern of carelessness that extends to the agency’s core operations.
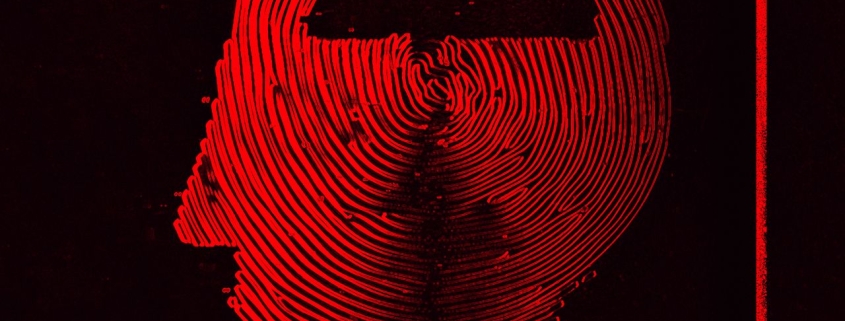
DHS Consolidates Surveillance Capabilities with Unified Database Initiative
The Department of Homeland Security has announced plans to combine its face and fingerprint recognition technologies into a centralized, searchable database accessible across all its agencies.
The initiative, which has raised significant privacy concerns among civil liberties advocates, aims to create a unified biometric identification system that would allow for rapid cross-referencing of facial recognition data with fingerprint records. Proponents argue that the system would enhance security and streamline law enforcement operations.
“Centralizing biometric data creates a single point of failure with enormous implications for privacy and civil liberties,” warns technology policy expert Dr. Robert Chen. “If this database is compromised, the consequences could be catastrophic.”
The plan has already drawn criticism from privacy advocates who point to the potential for mission creep and the risks associated with consolidating sensitive personal data in one location. Concerns have also been raised about the accuracy of facial recognition technology, particularly regarding its performance across different demographic groups.
Texas Drone Incident Highlights Challenges of Urban Airspace Security
Recent fears about possible drug cartel drone activity over Texas led to a temporary airspace shutdown in New Mexico and El Paso, Texas, highlighting the complex challenges of deploying anti-drone weapons near populated areas.
The incident, which disrupted commercial air traffic and raised public anxiety, ultimately underscored the technological and operational limitations of current counter-drone systems. Experts note that while the threat of weaponized or surveillance drones is real, the solutions available to address these threats often pose their own risks in urban environments.
“The challenge isn’t just detecting drones—it’s neutralizing them safely in areas where a misfire could cause civilian casualties or infrastructure damage,” explains aviation security specialist Maria Gonzalez. “We’re still in the early stages of developing effective, safe counter-drone capabilities for urban settings.”
The episode has prompted renewed calls for comprehensive drone regulation and the development of more sophisticated detection and mitigation technologies that can operate safely in complex airspace environments.
Massive Data Exposure Underscores Ongoing Identity Theft Risks
A database containing billions of records, including passwords and Social Security numbers, was left accessible to anyone online, highlighting the persistent threat of identity theft in the digital age.
Security researchers discovered the exposed database, which appeared to contain information from multiple sources aggregated into a single repository. While there was no evidence that the data had been actively exploited by criminals at the time of discovery, the sheer volume and sensitivity of the information made it an attractive target for identity thieves.
“This is far from an isolated incident,” notes cybersecurity researcher David Kim. “We’re seeing a pattern of organizations failing to properly secure sensitive data, creating ongoing risks for individuals whose information has been compromised.”
The incident has renewed calls for stronger data protection regulations and more robust security practices across industries that handle personal information. Experts emphasize that in an era of frequent data breaches, individuals need to assume their information may already be compromised and take appropriate protective measures.
$10,000 Bounty Offered for Ring Camera Privacy Hack
In an unusual move that highlights growing concerns about smart home device privacy, the Fulu Foundation—a nonprofit that pays bounties for removing user-hostile features—is offering $10,000 to anyone who can develop a method to use Ring cameras while preventing them from sending data to Amazon.
The challenge addresses one of the most significant privacy concerns surrounding Ring devices: their default configuration sends video footage and other data directly to Amazon’s servers, where it can be accessed by the company and, in some cases, shared with law enforcement agencies.
“Smart home devices have become surveillance tools that normalize constant monitoring,” says privacy advocate Lisa Chen. “This bounty represents a creative approach to reclaiming some measure of control over our personal spaces.”
The foundation is seeking technical solutions that would allow users to maintain the security benefits of Ring cameras while preventing data from being transmitted to Amazon’s servers. Potential approaches could include local storage solutions, network-level blocking, or hardware modifications that maintain functionality while enhancing privacy.
Robot Dogs Deployed for World Cup Security in Mexico
The Mexican city of Guadalupe, which will host portions of the 2026 World Cup, is preparing to deploy four new robot dogs to help provide security during matches at BBVA Stadium.
The quadrupedal robots, developed by Boston Dynamics, will be equipped with cameras, sensors, and communication systems to assist human security personnel in monitoring crowds and identifying potential threats. The deployment represents one of the largest-scale uses of robot dogs for public security purposes to date.
“While the technology offers interesting possibilities for enhancing security, it also raises questions about privacy and the normalization of surveillance,” notes technology ethicist Dr. James Wilson. “There’s a fine line between using robots to keep people safe and creating an atmosphere of constant monitoring.”
The use of robot dogs for security purposes has sparked debate about the appropriate role of autonomous systems in public spaces, particularly in the context of major international events where civil liberties concerns often come into sharp focus.
Tags and viral phrases:
FBI informant dark web fentanyl pills
Jeffrey Epstein Customs Border Protection ties
surveillance-resistant organizing digital privacy
DHS mega detention center metadata exposure
centralized biometric database face fingerprint
Texas drone airspace shutdown cartel threat
billions records Social Security numbers exposed
$10,000 Ring camera Amazon data hack bounty
robot dogs World Cup security Mexico 2026
password manager zero knowledge cryptographic flaws
Defcon Epstein banned Vincent Iozzo Joichi Ito
freedom.gov anti-censorship online portal VPN
mega trove exposed identity theft risks
robot dogs patrolling BBVA Stadium
FBI asset complicity fentanyl sales
Epstein network CBP officers US Virgin Islands
expert guide surveillance tools opsec
document metadata hidden data breach
DHS surveillance capabilities unified database
urban drone defense challenges populated areas
identity theft database billions records
smart home privacy Ring Amazon hack
Boston Dynamics robot dogs security deployment
cryptographic vulnerabilities password managers
Jeffrey Epstein cybersecurity community Defcon
online portal bypass content bans Europe
internet freedom programs funding shutdown
zero knowledge systems password manager flaws
mega detention processing centers exposed
counter-drone weapons urban environments
data breach personal information protection
local storage Ring camera privacy solution
autonomous security systems public spaces
mission creep biometric data consolidation
metadata trails digital collaboration security
user-hostile features smart home devices
fentanyl crisis dark web operations
civil liberties surveillance normalization
document handling procedures information security
facial recognition accuracy demographic bias
airspace security commercial flight disruption
identity protection data breach response
privacy-enhancing technologies smart devices
international events security robot deployment
cryptographic scrutiny password manager claims
government transparency metadata disclosure
drone regulation detection mitigation technology
personal space monitoring smart home debate
autonomous systems ethical considerations
data protection regulations industry standards
security benefits privacy trade-offs
civil liberties international sporting events
technology ethics public safety balance
digital rights advocacy surveillance culture
operational security activist organizing
biometric identification system privacy risks
counter-drone capabilities urban deployment
data aggregation identity theft prevention
network-level blocking smart device privacy
human security personnel robot assistance
content bans internet freedom regimes
government-funded internet programs shutdown
document revision history exposure
crowds monitoring autonomous security robots
surveillance tools normalization debate
protective measures data compromise
hardware modifications privacy enhancement
civil liberties concerns major events
surveillance-resistant workflows digital security
single point failure biometric database
misuse potential privacy implications
technical solutions data transmission blocking
Boston Dynamics quadrupedal security robots
major international events civil liberties
privacy advocate smart home surveillance
creative approaches personal data control
security personnel robot dog assistance
fine line safety monitoring atmosphere
appropriate role autonomous public systems
civil liberties focus international context
technology ethicist privacy surveillance balance
largest-scale robot dogs public security
constant monitoring smart home debate
reclaiming control personal spaces technology
security benefits privacy trade-offs devices
Boston Dynamics robot dogs deployment
international sporting events civil liberties
technology ethics public safety balance
digital rights advocacy surveillance culture
operational security activist organizing
biometric identification system privacy risks
counter-drone capabilities urban deployment
data aggregation identity theft prevention
network-level blocking smart device privacy
human security personnel robot assistance
content bans internet freedom regimes
government-funded internet programs shutdown
document revision history exposure
crowds monitoring autonomous security robots
surveillance tools normalization debate
protective measures data compromise
hardware modifications privacy enhancement
civil liberties concerns major events
surveillance-resistant workflows digital security
single point failure biometric database
misuse potential privacy implications
technical solutions data transmission blocking
Boston Dynamics quadrupedal security robots
major international events civil liberties
privacy advocate smart home surveillance
creative approaches personal data control
security personnel robot dog assistance
fine line safety monitoring atmosphere
appropriate role autonomous public systems
civil liberties focus international context
technology ethicist privacy surveillance balance
largest-scale robot dogs public security
constant monitoring smart home debate
reclaiming control personal spaces technology
security benefits privacy trade-offs devices
,



Leave a Reply
Want to join the discussion?Feel free to contribute!