Reverse Engineering Linux Distro REMnux Marks 15 Years With Major v8 Release Featuring AI Agent Support
REMnux v8 Unleashes Next-Level Malware Analysis with Agentic AI and Cutting-Edge Tools
In an era where Linux has become a lucrative target for bad actors, the cybersecurity landscape demands specialized tools more than ever. Enter REMnux v8, the latest evolution of the Linux distribution purpose-built for malware researchers and reverse engineers. While Kali Linux dominates the penetration testing space, REMnux carves its own niche by focusing exclusively on understanding malicious software at its core.
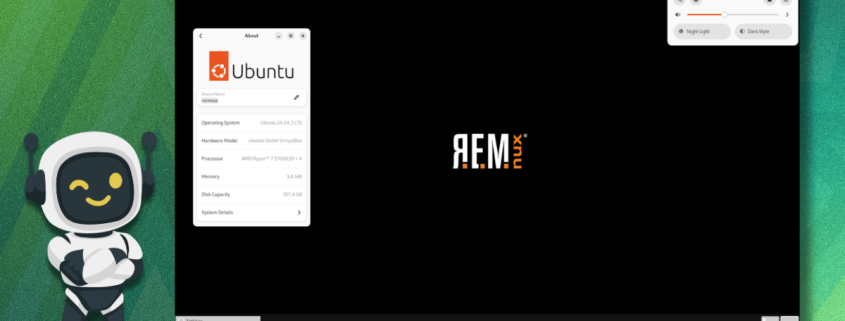
The Foundation: Ubuntu 24.04 LTS Powering Next-Gen Analysis
REMnux v8 builds upon the rock-solid foundation of Ubuntu 24.04 LTS, ensuring long-term support and stability for security researchers who need dependable tools. The upgrade introduces a revolutionary Cast-based installer that promises unprecedented reliability and seamless handling of system upgrades—a critical improvement for security professionals who can’t afford downtime.
Arsenal Expansion: 30+ New Tools for Modern Threats
The v8 release represents a quantum leap in analytical capabilities with dozens of new tools designed to tackle contemporary malware challenges:
Binary Analysis Revolution
- YARA-X: A complete Rust rewrite of the legendary YARA pattern matching engine, delivering 10x performance improvements and memory safety
- GoReSym & Redress: Specialized tools for dissecting Go binaries, addressing the explosive growth of Golang malware
- Manalyze & LIEF: Comprehensive PE, ELF, and MachO file parsers that can extract every hidden detail
Mobile and Document Threats
- APKiD: Android APK fingerprinting and analysis
- origamindee: Advanced PDF structure analysis for weaponized documents
- ZBar: QR code decoding for steganographic payloads
Scripting Language Warfare
- pyinstxtractor-ng: Unpacking PyInstaller-packed Python malware
- uncompyle6: Decompiling Python bytecode to recover source code
- AutoIt-Ripper: Analyzing AutoIt scripts commonly used in Windows malware
The AI Revolution: Agentic Intelligence in Malware Analysis
Here’s where REMnux v8 truly shatters expectations. The new MCP (Model Context Protocol) server creates a bridge between AI assistants like Claude and ChatGPT and REMnux’s entire toolkit. This isn’t just AI integration—it’s agentic AI that thinks, plans, and executes complex analysis workflows autonomously.
How It Works: Intelligent Analysis Orchestration
When presented with a Windows executable, the AI doesn’t just run one tool—it orchestrates a symphony of 16 different tools in perfect sequence. The process is remarkably sophisticated:
- Intelligent Planning: The AI analyzes the file type and determines the optimal analysis strategy
- Tool Selection: Based on file characteristics, it selects the most relevant tools from REMnux’s arsenal
- Execution Management: Tools run in the optimal order, with outputs feeding into subsequent analysis steps
- Result Correlation: The AI understands and synthesizes output from multiple tools, identifying patterns humans might miss
- Adaptive Response: When standard tools fail, the AI writes custom Python scripts on-the-fly for specialized tasks
Real-World Impact: Demonstrated by the Creator
Lenny Zeltser, REMnux’s visionary creator, has documented stunning demonstrations of this AI capability on his blog. The system successfully analyzed real-world malware samples that had stumped traditional analysis methods, identifying command-and-control infrastructure, decoding obfuscated configurations, and reconstructing malicious payloads—all with minimal human intervention.
Enhanced Tool Ecosystem
Beyond the MCP server, REMnux v8 enhances existing tools with AI capabilities:
- Ghidra: The NSA’s reverse engineering framework now features AI plugins for automated function identification and vulnerability discovery
- Radare2: Enhanced with AI-assisted disassembly and pattern recognition
- OpenCode: A terminal-based AI coding assistant that works seamlessly with the MCP server, allowing researchers to rapidly prototype analysis scripts
Installation Flexibility: Multiple Paths to Security
REMnux v8 offers unprecedented deployment flexibility:
Virtual Appliance: The Quick Start
The pre-configured virtual appliance can be imported directly into any major hypervisor (VMware, VirtualBox, KVM, Hyper-V) and is ready to use in minutes.
From Scratch Installation: Full Control
For those who prefer maximum customization, the install-from-scratch method allows installation on dedicated hardware or as a primary operating system.
Container Deployment: DevOps Friendly
Security teams can deploy REMnux as Docker containers, perfect for CI/CD pipelines and automated security testing environments.
Source Availability: Transparency
The entire distribution is open source on GitHub, allowing security researchers to audit, modify, and contribute to the project.
The Future of Malware Analysis
REMnux v8 represents more than just an update—it’s a paradigm shift in how we approach malware analysis. By combining the depth of traditional reverse engineering tools with the breadth and intelligence of AI, it empowers security researchers to tackle increasingly sophisticated threats.
The integration of agentic AI means that even junior analysts can perform complex analyses that previously required years of experience. Meanwhile, expert researchers can focus on the most challenging aspects of malware investigation while the AI handles routine analysis tasks.
As malware becomes more complex and targets become more diverse, tools like REMnux v8 will be essential weapons in the cybersecurity arsenal. Whether you’re defending corporate networks, researching emerging threats, or training the next generation of security professionals, REMnux v8 delivers the capabilities needed to stay ahead of malicious actors.
The question isn’t whether you need REMnux v8—it’s how quickly you can get it running in your environment.
Tags: REMnux v8, malware analysis, Linux security, AI-powered security, reverse engineering, cybersecurity tools, Ubuntu 24.04, agentic AI, malware research, threat analysis, digital forensics, security distribution, YARA-X, Ghidra AI, Radare2 AI, OpenCode, REMnux installation, cybersecurity innovation
Viral Phrases: “AI that thinks like a security researcher,” “16 tools in one click,” “malware analysis revolutionized,” “the future of digital forensics,” “security research supercharged,” “agentic intelligence meets malware analysis,” “Linux security never looked this good,” “defend against tomorrow’s threats today,” “the tool that bad actors fear,” “cybersecurity’s secret weapon,” “analysis that writes itself,” “AI-powered reverse engineering,” “the end of malware mysteries,” “security research at the speed of thought,” “malware analysis for the AI age”
,



Leave a Reply
Want to join the discussion?Feel free to contribute!