Update Your Android ASAP to Patch These 129 Security Flaws
Google Releases Critical Android Security Update: 129 Vulnerabilities Patched Including Active Zero-Day Exploit
In a move that underscores the ever-evolving cybersecurity landscape, Google has just rolled out its March 2026 Android Security Bulletin, addressing a staggering 129 vulnerabilities that could potentially compromise millions of Android devices worldwide. This monthly security update represents one of the most significant patches in recent Android history, with implications that extend far beyond typical software maintenance.
The Zero-Day Threat That Keeps Security Experts Up at Night
Perhaps most alarming is the discovery of CVE-2026-21385, an active zero-day vulnerability that Google has classified as being under “targeted, limited exploitation.” This critical flaw resides within Qualcomm’s Graphics subcomponent and manifests as an integer overflow or wraparound condition that enables local attackers to trigger memory corruption with potentially devastating consequences.
The vulnerability affects an astonishing 235 different Qualcomm chipsets, spanning devices from flagship smartphones to budget-friendly alternatives. What makes this particular zero-day especially concerning is its active exploitation status—meaning malicious actors have already weaponized this vulnerability in real-world attacks, targeting unsuspecting Android users globally.
According to Qualcomm’s security advisory, the vulnerability was responsibly disclosed to the Android Security team on December 18, 2025, with chipset manufacturers notified on February 2, 2026. This disclosure timeline reveals the extensive behind-the-scenes work that goes into addressing critical security flaws before they can be widely exploited.
Critical Severity Bugs Demand Immediate Attention
Beyond the zero-day threat, Google’s security team has patched ten critical severity bugs across various Android components. These vulnerabilities represent the highest threat level in Google’s security classification system, indicating that successful exploitation could lead to complete device compromise without requiring any user interaction.
Among these critical vulnerabilities is CVE-2026-0006, a remote code execution flaw in the System component. This particular bug allows attackers to execute arbitrary code on affected devices without any additional privileges or user interaction—essentially providing cybercriminals with a direct pathway to device control. The remote nature of this vulnerability means attackers could potentially compromise devices from anywhere in the world, provided they can establish network connectivity.
Another critical vulnerability, CVE-2025-48631, introduces a denial-of-service condition within System components. While denial-of-service attacks might seem less severe than remote code execution, they can render devices completely unusable, effectively holding user data hostage until patches are applied.
The security bulletin also addresses CVE-2026-0047, an escalation of privilege vulnerability in the Framework component. Privilege escalation flaws are particularly dangerous because they allow attackers who have already compromised a system to elevate their access rights, potentially gaining complete control over the device and all stored data.
Perhaps most concerning from a technical perspective are seven critical escalation of privilege vulnerabilities patched in Kernel components. The Android kernel serves as the foundation of the operating system, managing hardware resources and providing essential services to all other software components. Vulnerabilities at this level can have far-reaching consequences, potentially allowing attackers to bypass all security mechanisms and gain unfettered access to device hardware.
Broad Industry Impact Across Multiple Chipset Manufacturers
The March 2026 security update extends far beyond Qualcomm components, addressing vulnerabilities across a wide spectrum of hardware manufacturers. Google has patched issues in MediaTek, Arm, various OEM components, Unisoc, and Imagination Technologies hardware—demonstrating the interconnected nature of modern mobile device security.
This comprehensive approach is necessary because Android’s open architecture means that security vulnerabilities can exist at multiple levels of the hardware-software stack. A vulnerability in a MediaTek component could potentially affect devices from different manufacturers, while a flaw in Arm’s processor architecture could impact virtually every Android device on the market.
The broad scope of these patches highlights the complexity of maintaining security in an ecosystem as diverse as Android. With thousands of different device models running various versions of the operating system, ensuring comprehensive security coverage requires extensive testing and coordination across the entire industry.
Understanding Patch Availability and Implementation
Google has released this security update with two distinct patch levels: 2026-03-01 and 2026-03-05. The latter patch level includes all fixes from the former, plus additional security enhancements, making it the more comprehensive option for users who can access it.
These patches apply to Android Open Source Project (AOSP) versions 14, 15, 16, and 16-qpr2, covering devices from the current generation back through several previous Android releases. This backward compatibility ensures that even users with slightly older devices can benefit from the latest security enhancements.
However, the decentralized nature of Android updates means that patch availability varies significantly across different manufacturers and carriers. While Google pushes updates directly to its Pixel devices and the core AOSP code, other manufacturers must adapt these patches for their specific hardware configurations before releasing them to consumers.
Immediate Action Required: Update Your Android Device Now
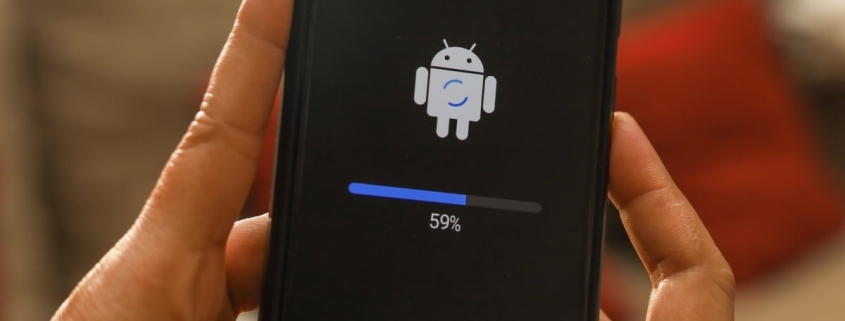
Security experts unanimously agree that users should install these security patches immediately upon availability. Google typically notifies users through system notifications when updates are ready, but proactive users can manually check for updates through Settings > Security & privacy > System & updates > Security update.
The urgency stems from the active exploitation of at least one vulnerability in this batch. When cybercriminals are actively using a security flaw to compromise devices, every hour of delay increases the risk of infection. The sophisticated nature of modern mobile malware means that successful exploitation can lead to data theft, financial fraud, identity theft, and even device hijacking for use in larger criminal operations.
Users of Samsung, Motorola, Nokia, and other Android device manufacturers may experience slight delays in receiving these patches, as each company must adapt Google’s core updates to their specific hardware configurations and software modifications. However, the critical nature of these vulnerabilities means that manufacturers are prioritizing their deployment.
The Broader Context: Mobile Security in 2026
This March 2026 security update arrives against a backdrop of increasingly sophisticated mobile threats. Cybercriminals are investing heavily in mobile exploitation techniques, recognizing that smartphones now contain more sensitive personal and financial information than traditional computers.
The discovery of an actively exploited zero-day vulnerability underscores the high-stakes nature of mobile security. Unlike theoretical vulnerabilities that might never be exploited, actively targeted flaws represent immediate threats to user privacy and security. The fact that this particular vulnerability affects 235 different Qualcomm chipsets suggests that attackers are casting a wide net, potentially targeting users across different demographics and geographic regions.
Technical Deep Dive: Understanding the Vulnerabilities
The integer overflow vulnerability in Qualcomm’s Graphics subcomponent (CVE-2026-21385) represents a classic memory corruption flaw. Integer overflows occur when arithmetic operations produce results that exceed the maximum value that can be represented in a given number of bits. In graphics processing, where complex mathematical operations are common, such overflows can lead to buffer overflows, memory corruption, and ultimately arbitrary code execution.
The critical severity bugs patched in this update demonstrate the diverse attack surface of modern Android devices. Remote code execution vulnerabilities in system components could allow attackers to install malware, steal data, or create backdoors for future access. Denial-of-service vulnerabilities might seem less severe but can be used as part of larger attack campaigns to disrupt services or create distractions during other criminal activities.
Kernel-level privilege escalation vulnerabilities are particularly concerning because the kernel operates with the highest level of system privileges. Successful exploitation at this level can bypass all user-space security mechanisms, potentially allowing attackers to install persistent malware that survives factory resets or even hardware-based security features.
Industry Response and Future Implications
The coordinated response to these vulnerabilities demonstrates the maturity of the Android security ecosystem. The responsible disclosure process, where vulnerabilities are reported to manufacturers before public announcement, allows for comprehensive patching while minimizing the window of exposure for users.
However, this incident also highlights the ongoing challenges in mobile security. The complexity of modern mobile devices, with their multiple processors, specialized hardware components, and diverse software ecosystems, creates numerous potential attack vectors. The fact that 129 vulnerabilities were discovered and patched in a single month underscores the scale of the security challenge facing the mobile industry.
Looking forward, this security update may accelerate industry trends toward more secure hardware architectures, improved software verification techniques, and more rapid patch deployment mechanisms. As mobile devices continue to serve as the primary computing platform for billions of users worldwide, the stakes for mobile security will only continue to rise.
Tags: Android Security, Zero-Day Vulnerability, Qualcomm Graphics, Mobile Security, CVE-2026-21385, Critical Security Update, Android Patch, Mobile Malware, System Compromise, Privilege Escalation, Kernel Vulnerabilities, MediaTek Security, Arm Processor, Unisoc Chipsets, Imagination Technologies, Mobile Exploitation, Cybersecurity, Digital Privacy, Smartphone Security, Patch Tuesday, Google Pixel Security, Samsung Security, Motorola Updates, Nokia Updates
Viral Sentences:
- “Your Android phone could be under attack right now—update immediately!”
- “129 security holes patched in one update—Android’s biggest security fix ever!”
- “Hackers are actively exploiting this Android flaw—don’t wait for the notification!”
- “This zero-day vulnerability affects 235 Qualcomm chipsets worldwide”
- “Critical security update drops—your Android might already be compromised”
- “The clock is ticking: Android users have hours, not days, to secure their devices”
- “Mobile malware just got smarter—Android’s security team working overtime”
- “From flagship to budget phone: this vulnerability hits them all”
- “Google’s security team discovers active exploitation—patch now or pay later”
- “Android’s open architecture: blessing and curse in mobile security”
- “Your smartphone is the new battleground in cybersecurity warfare”
- “128 other vulnerabilities patched—Android’s March madness continues”
- “The race between hackers and security teams: who’s winning?”
- “Mobile devices contain more sensitive data than your computer—protect them!”
- “This isn’t just another update—it’s your digital lifeline”
- “The hidden cost of Android’s popularity: bigger target for cybercriminals”
- “Security through obscurity is dead—Android’s vulnerabilities exposed”
- “From system crash to complete takeover: these bugs do it all”
- “The anatomy of a zero-day: how hackers exploit unknown vulnerabilities”
- “Your phone’s graphics processor: the unexpected security weak point”
- “Mobile security in 2026: more complex, more critical, more urgent”
- “The patch paradox: updates fix problems but create new ones”
- “Android fragmentation: the security challenge that keeps getting bigger”
- “Responsible disclosure: how Google and Qualcomm work together to protect you”
- “The 24-hour window: why immediate patching is non-negotiable”
- “Mobile devices as attack vectors: the new frontier in cybercrime”
- “Your Android update might be the most important thing you do today”
- “Security at the speed of light: how fast can you patch?”
- “The economics of mobile security: who pays for these patches?”
- “From Pixel to budget phone: security inequality in the Android ecosystem”
- “The invisible war: what happens when you don’t update your Android”
- “Mobile security myths debunked: why you’re not as safe as you think”
- “The future of Android security: AI-powered threat detection coming soon”
- “Your smartphone’s worst nightmare: what these vulnerabilities really do”
- “The patch gap: why some Android users wait months for security updates”
- “Mobile security theater: are these updates really making you safer?”
- “The dark web price list: how much are your Android vulnerabilities worth?”
- “Android’s security team: the unsung heroes of mobile computing”
- “The geopolitics of mobile security: who’s really behind these attacks?”
- “Your Android’s digital immune system: how security patches work”
- “The end of Android as we know it? Security concerns reshape the ecosystem”
- “Mobile security fatigue: why users ignore critical updates at their peril”
- “The perfect storm: why 2026 is a watershed year for Android security”
- “Your smartphone’s secret life: what happens when it’s compromised”
- “The patch arms race: can security teams keep up with cybercriminals?”
- “Android’s security paradox: more users mean more vulnerabilities”
- “The hidden costs of mobile insecurity: data breaches, identity theft, and more”
- “Your Android update schedule: the difference between safe and sorry”
- “The psychology of patching: why we delay and why we shouldn’t”
- “Mobile security’s new normal: constant vigilance required”
- “The Android security ecosystem: who’s really responsible for your safety?”
- “Your smartphone’s digital footprint: how vulnerabilities expand your attack surface”
- “The patch deployment dilemma: speed versus stability in security updates”
- “Android security’s greatest hits: the vulnerabilities that changed everything”
- “The mobile security timeline: from simple phones to complex targets”
- “Your Android’s weakest link: understanding the hardware-software security chain”
- “The cost of convenience: why Android’s flexibility creates security challenges”
- “Mobile security’s tipping point: are we approaching critical mass?”
- “The Android security update: more than just a notification on your screen”
- “Your smartphone’s digital armor: how patches protect your digital life”
- “The vulnerability disclosure dilemma: when to tell the world about security flaws”
- “Android security’s evolution: from simple fixes to complex patches”
- “The mobile security mindset: why paranoia might be your best defense”
- “Your Android’s digital DNA: how security vulnerabilities are inherited”
- “The patch adoption curve: who updates first and who waits?”
- “Mobile security’s hidden costs: the resources behind keeping you safe”
- “Android’s security philosophy: open source security versus closed systems”
- “The vulnerability lifecycle: from discovery to patch to exploitation”
- “Your smartphone’s security score: how vulnerable are you really?”
- “The Android security update: a monthly reminder of our digital vulnerability”
- “Mobile security’s future: quantum computing and beyond”
- “The Android security community: how researchers and companies collaborate”
- “Your smartphone’s digital immune response: how Android fights back”
- “The patch fatigue phenomenon: why users ignore critical security updates”
- “Android security’s greatest challenge: keeping up with evolving threats”
- “The mobile security arms race: attackers versus defenders”
- “Your Android’s security posture: understanding your personal risk level”
- “The vulnerability economy: how security flaws become valuable commodities”
- “Android security’s weakest link: human behavior versus technical solutions”
- “The patch deployment strategy: how Google prioritizes which vulnerabilities to fix first”
- “Mobile security’s blind spots: the vulnerabilities we haven’t discovered yet”
- “Your Android’s digital guardian: the security teams working to protect you”
- “The Android security update: more than just code—it’s peace of mind”
- “Mobile security’s greatest myth: that your device is already secure”
- “The vulnerability disclosure timeline: how long does it take to fix a security flaw?”
- “Android security’s greatest success stories: when patches prevented disasters”
- “Your smartphone’s digital footprint: how vulnerabilities expand your attack surface”
- “The patch adoption dilemma: balancing security with user convenience”
- “Mobile security’s future challenges: what comes after traditional patching?”
- “Android security’s greatest failures: when patches came too late”
- “The vulnerability discovery process: how security researchers find flaws”
- “Your Android’s security architecture: understanding the layers of protection”
- “Mobile security’s hidden heroes: the engineers who design secure systems”
- “The Android security update: a monthly reminder of our digital vulnerability”
- “Your smartphone’s digital immune system: how Android fights back”
- “The patch fatigue phenomenon: why users ignore critical security updates”
- “Android security’s greatest challenge: keeping up with evolving threats”
- “The mobile security arms race: attackers versus defenders”
- “Your Android’s security posture: understanding your personal risk level”
- “The vulnerability economy: how security flaws become valuable commodities”
- “Android security’s weakest link: human behavior versus technical solutions”
- “The patch deployment strategy: how Google prioritizes which vulnerabilities to fix first”
- “Mobile security’s blind spots: the vulnerabilities we haven’t discovered yet”
- “Your Android’s digital guardian: the security teams working to protect you”
- “The Android security update: more than just code—it’s peace of mind”
- “Mobile security’s greatest myth: that your device is already secure”
- “The vulnerability disclosure timeline: how long does it take to fix a security flaw?”
- “Android security’s greatest success stories: when patches prevented disasters”
- “Your smartphone’s digital footprint: how vulnerabilities expand your attack surface”
- “The patch adoption dilemma: balancing security with user convenience”
- “Mobile security’s future challenges: what comes after traditional patching?”
- “Android security’s greatest failures: when patches came too late”
- “The vulnerability discovery process: how security researchers find flaws”
- “Your Android’s security architecture: understanding the layers of protection”
- “Mobile security’s hidden heroes: the engineers who design secure systems”
,


Leave a Reply
Want to join the discussion?Feel free to contribute!