WireGuard Is Two Things – Proxylity Blog
Here’s the rewritten news article with a more detailed, tech-savvy, and viral tone:
WireGuard: The Encryption Protocol You Didn’t Know You Needed
<!-- VPN App box -->
<rect x="30" y="25" width="285" height="72" rx="8" fill="none" stroke-width="2" opacity="0.75"/>
<text x="172" y="57" text-anchor="middle" font-size="15" font-weight="600">WireGuard VPN App</text>
<text x="172" y="78" text-anchor="middle" font-size="11" opacity="0.6">wg · network-manager ·
tunnelblick</text>
<!-- Your App box -->
<rect x="385" y="25" width="285" height="72" rx="8" fill="none" stroke-width="2" opacity="0.75"/>
<text x="527" y="57" text-anchor="middle" font-size="15" font-weight="600">Your Application</text>
<text x="527" y="78" text-anchor="middle" font-size="11" opacity="0.6">WireGuardClient · any UDP
workload</text>
<!-- Connector lines -->
<line x1="220" y1="97" x2="265" y2="152" stroke-width="1.5" opacity="0.45" stroke-dasharray="5,3"/>
<line x1="480" y1="97" x2="435" y2="152" stroke-width="1.5" opacity="0.45" stroke-dasharray="5,3"/>
<!-- Protocol box (highlighted) -->
<rect x="55" y="152" width="590" height="82" rx="8" fill-opacity="0.12" stroke-width="2.5" opacity="0.9"/>
<text x="350" y="185" text-anchor="middle" font-size="17" font-weight="700">WireGuard
Protocol</text>
<text x="350" y="210" text-anchor="middle" font-size="12" opacity="0.65">Noise Protocol Framework
· ChaCha20-Poly1305 · Stateless · No PKI</text>
<!-- Connector line to UDP -->
<line x1="350" y1="234" x2="350" y2="265" stroke-width="1.5" opacity="0.45" stroke-dasharray="5,3"/>
<!-- UDP box -->
<rect x="215" y="265" width="270" height="52" rx="8" fill="none" stroke-width="2" opacity="0.75"/>
<text x="350" y="296" text-anchor="middle" font-size="14" font-weight="600">UDP Datagrams</text>
</g>
</svg>
</p><div>
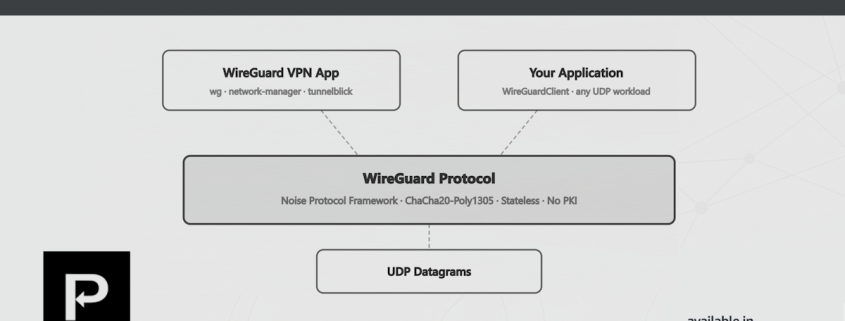
<p>Ask a developer what WireGuard is, and you'll almost certainly hear: "It's a VPN." That's accurate, but
it's only half the answer — and the less interesting half.</p>
<p>WireGuard is actually two things:</p>
<ul>
<li><strong>A VPN application</strong> — the <code>wg</code> tool, kernel module, and associated
ecosystem that creates encrypted network tunnels between machines. This is what most people use, and
what most articles describe.</li>
<li><strong>A cryptographic protocol</strong> — a clean, modern specification built on the Noise
Protocol Framework and ChaCha20-Poly1305, designed to encrypt UDP datagrams. This part is
independent of VPNs, IP tunneling, and routing tables entirely.</li>
</ul>
<p>The protocol is where the interesting engineering lives. And it turns out you can use it as a library —
as a drop-in encryption layer for any application that moves data over UDP — without running a VPN at
all. We just open sourced a .NET library that does exactly that.</p>
<h2>Why This Matters: Problems with TCP</h2>
<p>Before getting into what the library does, it's worth being honest about why we need better options here.
The standard answer to "I need encrypted transport" is TLS over TCP, and it works well for a large class
of problems. But TCP has structural costs that show up as real user-facing issues whenever latency,
mobility, or lossy links are involved. Three in particular keep coming up in support queues.</p>
<h3>Head-of-line blocking</h3>
<p>TCP guarantees ordered delivery. When a single packet is lost in transit, every subsequent packet waits
in a queue until the missing one is retransmitted — even if those later packets have already arrived.
For a telemetry stream, game state update, or sensor reading, you almost certainly don't care about
ordering. You want the latest value. TCP gives you stale data delivered in strict sequence.
</p><p>The symptom is familiar: a stream that occasionally "locks up" briefly before catching up, jitter in
audio or video, or a latency spike that appears to come from nowhere, a "hang" in the application when
it gets blocked waiting for a packet. It comes from a single packet
forcing the entire pipeline to pause. The underlying network recovered quickly; TCP's ordering guarantee
is what made it visible.</p>
<h3>Connection state resets</h3>
<p>TCP connections are tied to a 4-tuple: source IP, source port, destination IP, destination port. When a
mobile client roams from Wi-Fi to cellular, its IP address changes, every open TCP connection is torn
down, and the TLS session with it. Your application absorbs the cost of reconnecting, re-negotiating
TLS, and re-establishing application-level state.</p>
<p>For devices that move — phones, vehicles, field equipment — this isn't an edge case. It's routine. The
RST arrives, the error propagates up the stack, and somewhere a retry loop starts counting. If you've
ever wondered why a mobile app occasionally takes an extra few seconds to,



Leave a Reply
Want to join the discussion?Feel free to contribute!