Your password manager isn’t as safe as you think
Popular Password Managers Bitwarden, LastPass, and Dashlane Found Vulnerable to Serious Security Flaws
In a shocking revelation that has sent ripples through the cybersecurity community, researchers from ETH Zurich and the Università della Svizzera italiana (USI) in Lugano have uncovered critical security vulnerabilities in three of the most widely-used password managers: Bitwarden, LastPass, and Dashlane. These findings challenge the long-held belief that password managers are impenetrable fortresses for our digital credentials.
The Shocking Discovery
The research team discovered that these password managers, which millions of users trust to safeguard their most sensitive information, contain serious security flaws that could potentially expose stored passwords to unauthorized access and even manipulation. In their tests, the researchers were able to view and modify stored passwords, raising serious questions about the fundamental security architecture of these popular services.
“We were able to demonstrate that these password managers are less secure than previously believed,” stated the research team. “The vulnerabilities we discovered range from breaches of user vault integrity to complete compromise of organizational accounts.”
Why Are These Password Managers Vulnerable?
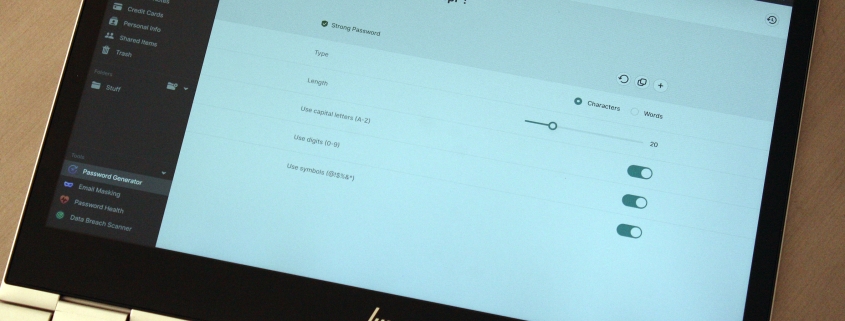
The core issue lies in how these password managers handle encryption and data storage. While all three services encrypt passwords in the cloud—allowing users to access their credentials across multiple devices—the researchers found that the encryption implementations contain critical weaknesses.
The team demonstrated an alarming 12 different attack vectors against Bitwarden, 7 against LastPass, and 6 against Dashlane. To conduct these tests, they created simulated environments that mimicked compromised password manager servers and then initiated routine user interactions such as logging in, opening vaults, viewing passwords, and synchronizing data.
What makes these vulnerabilities particularly concerning is their accessibility. According to the researchers, these attacks don’t require sophisticated computing resources or advanced technical knowledge. “These attacks don’t require particularly powerful computers and servers, just small programs that can spoof the server’s identity,” they explained.
The Root Cause: Outdated Encryption Methods
The fundamental problem, according to the researchers, stems from password manager developers’ reluctance to update their cryptographic systems. This hesitation is driven by a legitimate concern: millions of individual users and thousands of companies rely on these services for their entire password management infrastructure. A sudden system update that renders passwords inaccessible could have catastrophic consequences.
As a result, many providers continue to use cryptographic technologies from the 1990s, despite these methods being long outdated and vulnerable to modern attack techniques. The researchers described encountering “very bizarre code architectures” that were likely created in attempts to balance user-friendliness with security—allowing features like password recovery and family account sharing.
These complex architectures create multiple potential attack points, making the systems more vulnerable than simpler, more modern implementations would be.
The Response from Password Managers
Before publishing their findings, the research team responsibly disclosed the vulnerabilities to each affected password manager, giving them time to develop and implement fixes. While all three companies responded positively to the disclosure, the speed of their responses varied significantly.
The researchers emphasized that while these vulnerabilities are serious, there’s no evidence that any password manager provider is currently malicious or compromised. “As long as this remains the case, your passwords are safe,” they assured users. However, they also noted that password managers represent high-profile targets, and security breaches do occur with alarming frequency.
What Should Users Do?
For users concerned about their password security, the researchers recommend several precautionary measures:
- Choose password managers that openly disclose potential security vulnerabilities
- Select services that undergo regular external security audits
- Ensure end-to-end encryption is enabled by default
- Stay informed about security updates and apply them promptly
The researchers also suggest that the industry needs to move toward a model where new customers receive updated, more secure systems, while existing customers can choose whether to migrate to the new system or remain with the older, less secure version—making an informed decision about the trade-offs involved.
Industry-Wide Implications
This research has broader implications for the entire password management industry. It highlights the tension between maintaining backward compatibility and ensuring cutting-edge security. As cyber threats become increasingly sophisticated, the industry may need to make difficult decisions about when to force updates that could potentially disrupt service but significantly enhance security.
The findings also underscore the importance of regular security audits and the need for transparency in how password managers handle encryption and user data. Users should demand clear communication from their password managers about security practices and potential vulnerabilities.
Expert Recommendations
Security experts recommend that users currently using Bitwarden, LastPass, or Dashlane should:
- Monitor official communications from their password manager for security updates
- Enable two-factor authentication wherever possible
- Consider diversifying their password management approach
- Regularly review and update their stored credentials
While the immediate danger may be limited, the discovery of these vulnerabilities serves as a wake-up call for both users and providers in the password management ecosystem.
Looking Forward
The password management industry now faces a critical juncture. The research from ETH Zurich and USI has exposed fundamental weaknesses that cannot be ignored. Moving forward, providers will need to balance the competing demands of security, usability, and backward compatibility.
For users, this research serves as a reminder that no security solution is perfect, and vigilance remains essential in protecting digital credentials. As the industry responds to these findings, users should stay informed and make security-conscious decisions about their password management practices.
The full research paper detailing these vulnerabilities is expected to be published in the coming months, and the cybersecurity community will undoubtedly be watching closely to see how the industry responds to these critical findings.
Tags & Viral Phrases: password manager security flaws, Bitwarden hacked, LastPass vulnerability, Dashlane breach, cybersecurity researchers discover, ETH Zurich security findings, password manager encryption broken, cloud password storage risks, 1990s encryption outdated, password manager vulnerabilities exposed, digital security crisis, master password compromise, vault encryption failure, password manager warning, cybersecurity experts sound alarm, data breach risk, password security emergency, online security threat, encryption vulnerability discovered, password manager warning signs, digital identity protection, cybersecurity research breakthrough, password manager investigation, security audit reveals flaws, end-to-end encryption problems, password manager industry shaken, cybersecurity community reacts, digital security experts warn, password manager users alerted, security researchers uncover, password management crisis, encryption technology outdated, password manager security update needed, cybersecurity vulnerability report, password manager users beware, digital security landscape changing, password manager industry response, cybersecurity findings published, password manager security debate, digital security best practices, password manager alternatives, cybersecurity protection measures, password manager security comparison, digital security recommendations, password manager user guide, cybersecurity awareness campaign, password manager security checklist, digital security solutions
,


Leave a Reply
Want to join the discussion?Feel free to contribute!